Overview
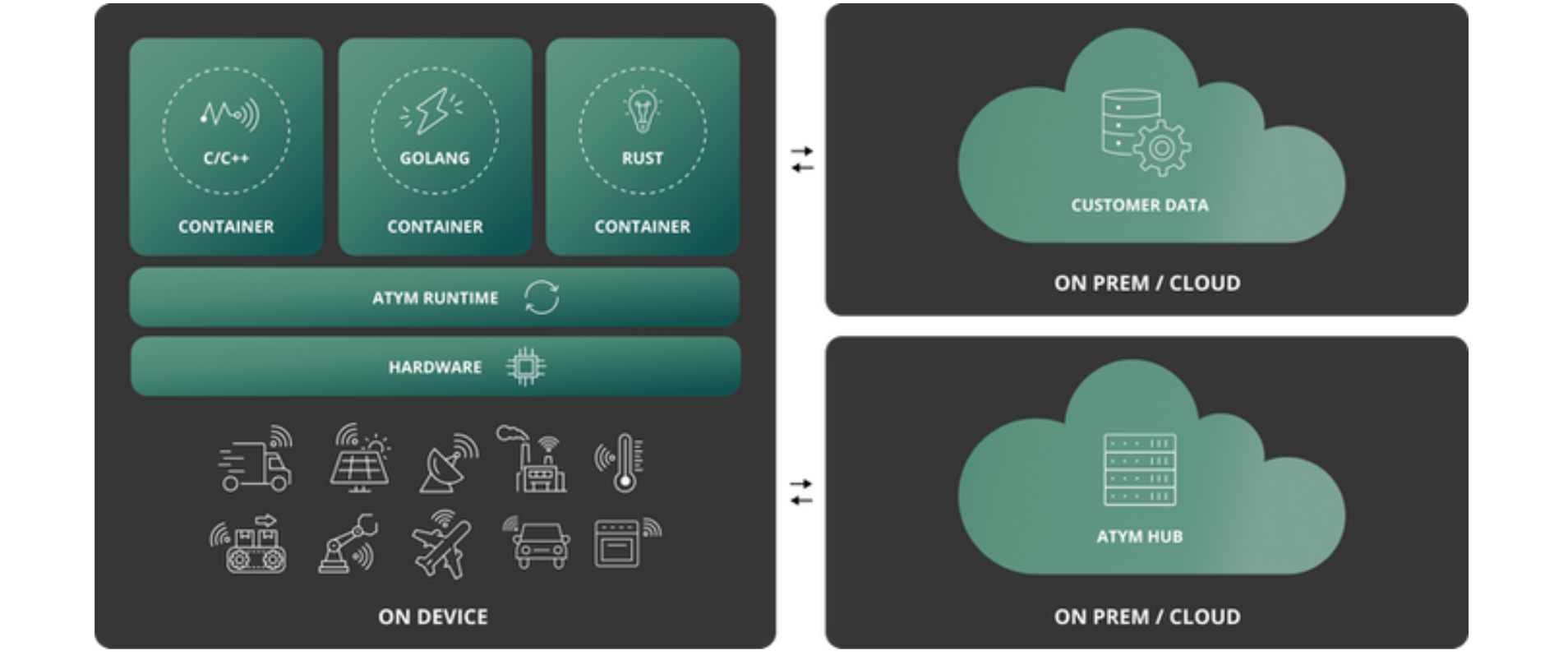
Atym is an enterprise-grade edge orchestration platform that brings cloud-native development, deployment, and security models to resource-constrained devices.
At its core, Atym applies OCI-inspired containerization principles to the edge by leveraging WebAssembly (Wasm) in place of traditional container engines that are impractical on many edge devices. This decouples application delivery from hardware, operating system, and firmware lifecycles, enabling independent deployment, updates, and security boundaries.
This allows teams to treat edge devices more like cloud infrastructure: modular, updatable, and manageable at scale.
Where Atym Fits
The challenge at the edge is not the extremes, but the middle: devices that are too resource-constrained for traditional container platforms, yet still require modular application delivery, strong isolation, and fleet-scale management.
Atym is designed specifically for this gap, supporting hardware that ranges from ARM Cortex-M3 class microcontrollers and above (~256KB RAM) to embedded Linux systems that that cannot efficiently run Docker. While optimized for constrained edge deployments, Atym’s container model remains fully portable and can also be used in cloud environments, preserving architectural consistency across the stack.
Rethinking Embedded Development
Traditional embedded systems tightly couple application logic, hardware, and firmware. This results in:
- monolithic builds,
- complex cross-compilation workflows,
- full firmware updates for small changes,
- and brittle supply-chain dependencies between teams and partners.
These same characteristics also make security difficult to reason about and maintain—especially as edge devices become increasingly connected and subject to regulatory scrutiny.
Atym breaks this model.
Using an on-device runtime, Atym abstracts hardware and operating system details, enabling applications to be delivered as isolated, portable containers that can be deployed and updated independently—without reflashing firmware. This approach brings proven cloud-native security practices, such as container signing, software bills of materials (SBOMs), and explicit trust boundaries, to this class of devices. Each application runs in a sandboxed environment with strong memory isolation and controlled access to system resources, reducing blast radius and simplifying compliance with emerging security and resilience regulations.
This architectural shift enables a set of cloud-era capabilities at the physical edge:
-
Application Portability - applications are built once and run consistently across heterogeneous hardware—from microcontrollers to embedded Linux—using standard languages that compile to WebAssembly.
-
Fractional Updates - applications can be updated at the component level, eliminating the need for full firmware rebuilds and enabling faster, lower-risk over-the-air updates.
-
Enterprise-Grade Security - strong isolation, memory safety, and zero-trust principles—rooted in hardware and enforced by the runtime—support modern compliance requirements such as the Cyber Resilience Act (CRA) and SBOM mandates.
-
Resource Efficiency - the Atym runtime is optimized for constrained environments avoid the overhead of traditional container platforms, saving hundreds of megabytes on Linux devices and enabling containerized workflows on microcontrollers.
-
Scalable Fleet Management - applications and devices can be managed at fleet scale using cloud-like operational models, without sacrificing the constraints and realities of embedded systems.
-
Open Standards, Open Core -built on WebAssembly, Zephyr RTOS, CoAP, and OCI-inspired packaging, Atym avoids vendor lock-in while providing a clear path to enterprise support and long-term maintainability.
Solution Components
Atym is built around a simple but deliberate architecture: a centralized control plane paired with a lightweight, on-device runtime. Together, these two components form the Atym platform. Applications are delivered through an OCI-compliant container model designed specifically for resource-constrained edge environments.
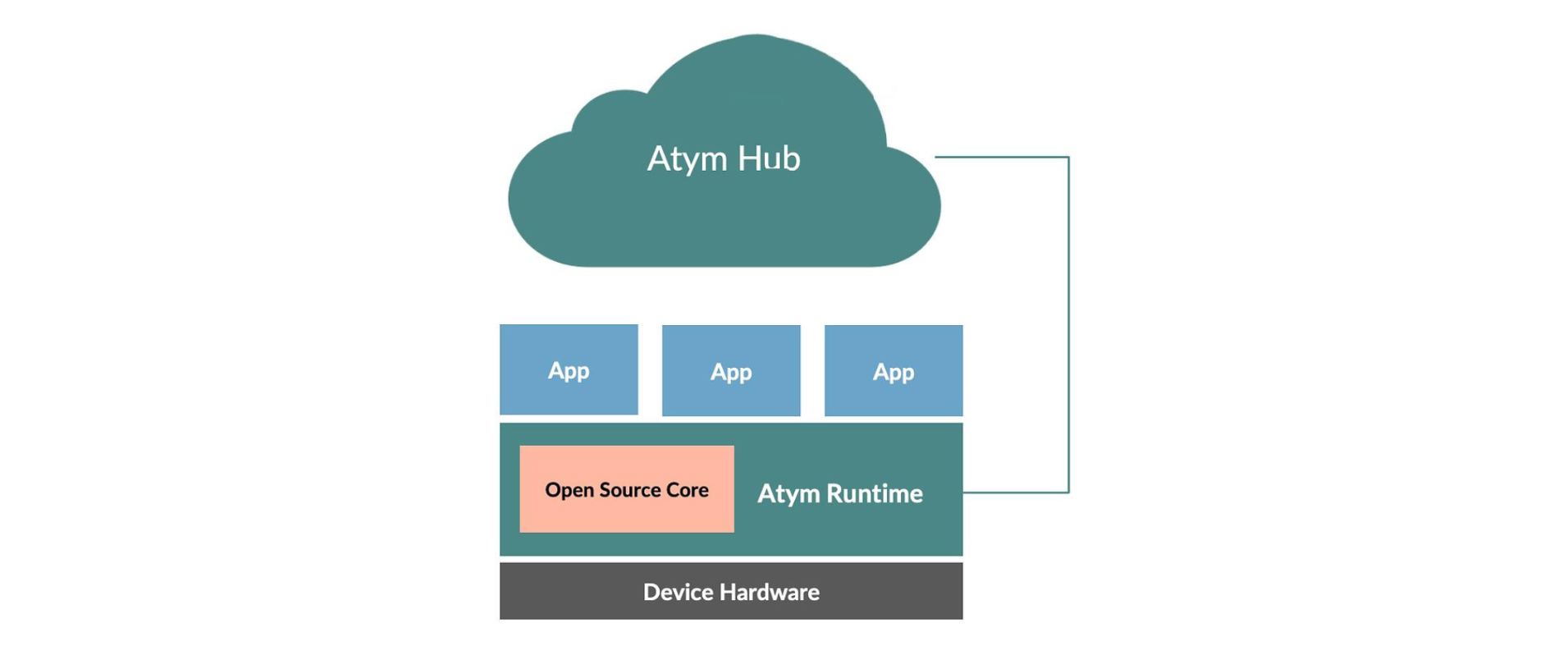
At the center of the platform is Atym Hub, the management and control plane for the system. The Atym Hub provides the interfaces and automation required to manage applications, devices, and fleets at scale. Through the Hub, teams can deploy and update workloads, monitor device and application health, and enforce security and policy across their edge fleets. Atym Hub is offered as a SaaS by default, with options for private cloud and on-prem deployments to support different operational and regulatory requirements.
Running on each device is the Atym Runtime, a lightweight execution environment responsible for running application workloads and enforcing isolation and security boundaries. The runtime uses WebAssembly (Wasm) as its execution and isolation technology, providing a consistent application model across heterogeneous hardware architectures and instruction sets. By abstracting hardware and operating system details, the Atym Runtime provides a stable execution target with a consistent application binary interface (ABI) across heterogeneous devices. The runtime enforces resource controls, memory isolation, and access boundaries on a per-application basis at execution time.The runtime follows an open-core model and is hosted by the Linux Foundation (Ocre), with enterprise support, lifecycle management, and platform integration provided through Atym Hub.
Applications are delivered using Atym Containers, the unit of application packaging and delivery within the platform. Atym Containers are OCI-compliant and leverage existing container concepts, workflows, and tooling wherever possible. They bundle application code and metadata into portable workloads optimized for constrained environments, providing familiar container semantics—such as packaging, versioning, signing, and isolation—at a fraction of the footprint required by traditional container platforms. This allows applications to be developed, deployed, and updated independently of device firmware and hardware lifecycles.
Together, these components enable a cloud-like operational model at the edge, without imposing cloud-scale assumptions on constrained devices.
The Atym Application Model
Atym adopts an application model that will feel familiar to developers accustomed to working with traditional OCI-based containers. Applications are packaged, versioned, signed, deployed, and updated as independent units using standard OCI image formats and registries, following the same core concepts and workflows used with traditional container platforms.
This decoupled model enables component-level integration rather than source-level integration. Applications are delivered and composed as independently built containers, eliminating the need to compile all functionality into a single monolithic image. As a result, internal teams and external partners can independently build, ship, and maintain applications—while preserving clear intellectual property boundaries, strong security guarantees, and operational consistency across device fleets.
From a developer perspective, the Atym programming model is aligned with POSIX, enabling developers to leverage existing knowledge, code, and practices. Applications interact with the runtime through familiar system abstractions that provide a portable foundation for common operating system functionality. Atym extends this foundation to support the needs of real-world edge applications while preserving a consistent and predictable execution model.
Because POSIX behavior varies across implementations, Atym aligns its interfaces and semantics with Linux, which has effectively become the de facto reference implementation. This approach minimizes surprises, reduces porting effort, and allows developers to apply established Linux practices when building applications.